Security is about more than million-dollar firewalls; usually, it’s about the small, daily habits that keep small issues from escalating into major problems. These days, the lines between personal and professional lives are blurrier than ever, and a compromised personal device could also mean access to an entire corporate network.
IT Support Business Models by Macro Systems
Even in its simplest form, a small business is a complex machine. One cog that’s not operating at the appropriate capacity can create operational problems that lead to bigger, more expensive problems later down the road. While businesses worry about the economy and ensuing financial issues, the reality is that your business is far more likely to fail due to operational inefficiencies.
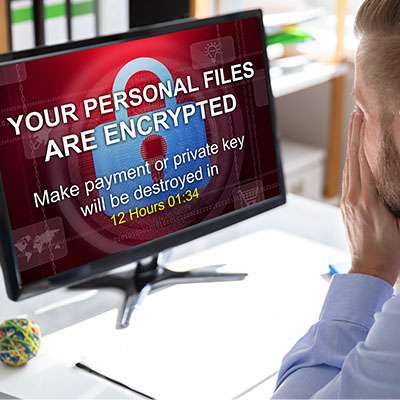
We usually hear one specific misconception more than any other: Why would a hacker care about my small operation when they could go after a Fortune 500 company?
The reality is much grimmer. Cybercriminals don't just target small businesses; they prefer them. Small to mid-sized businesses (SMBs) often serve as soft targets with weaker defensive perimeters and fewer dedicated security resources. For a hacker, it’s the difference between trying to crack a bank vault and walking through an unlocked screen door.
In its current state, artificial intelligence takes whatever you tell it very literally. As such, it is very easy to misdirect it into digital rabbit holes… which is the last thing you want, when time is very much money to your business. This is exactly why it is so imperative that we become adept at properly prompting the AI models we use. Too many hallucinations (responses that share inaccurate or unreliable information) simply waste time and money, but the better the prompt, the less prone the AI will be to hallucinate.
Listed below are some of the best practices to keep in mind as you draft your prompts.
Starting a small business is exciting but keeping it running is the real challenge. Many businesses start with a great idea, a solid customer base, and high hopes, only to crash and burn because of avoidable mistakes. If you’re a small business owner or planning to become one, look out for these three major pitfalls that can sink your business faster than you can say bankruptcy.
“I don’t need to worry about cyberattacks… my business is too small to be of any interest.”
This brief rationalization is one of the most dangerous fallacies a modern business can make concerning cybersecurity; it shows a fundamental misunderstanding of how modern cyberthreats operate. If this has been your mindset, we urge you to read on so we can help set you on a more realistic path.
With technology being such a massive part of modern business, many organizations are looking to use it to their advantage. One aspect of the business that is increasingly significant is their ability to stand out amongst their competition. Listed below are a few technologies that can enhance your organizational marketing efforts.
The last few weeks have been spent discussing ransomware's impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To conclude, we want to take a look at ransomware's impacts on society, specifically regarding economic health and geopolitical security, known as third-order harms.
It can be too easy to look at ransomware as a business problem; it does attack businesses, locking down their data for ransom, usually selling it or spreading it, and sometimes altering it for the business if returning it at all. It can be too easy to overlook another impacted target in all the mess.
What happens to the people whose data a business has collected and uses?
Businesses require a certain degree of good fortune to continue to grow in the manner in which they project when they hang out their shingle. With so many businesses failing after a very short time, taking advantage of the opportunities you’re given is extremely important. In this month’s newsletter, we’ll go through some of the things that a business can do to take better advantage of some opportunities.
Professional services make up a significant portion of the business landscape. They can be broadly defined as any company with trained professionals at the center offering a service of note. The most common professionals under this umbrella term are lawyers, agents, consultants, and others who help businesses in their day-to-day operations. Listed below are some of the technologies that fuel professional service providers.
This goes out to all the business owners, managers, department heads, and other leaders in the workplace who have to field user complaints and issues.
Being in this position can be difficult, because you often have to say no. No, we can’t change the timeline or increase the budget for this project. No, we can’t do XYZ that way because it would break compliance. No, we can’t get new hardware/software in until we get it approved in the budget. Repeat ad nauseam.
How often does your organization take it upon itself to ensure that those working for its success—your employees—are kept up to speed on cybersecurity? If your approach is to have your team sit in a room and watch a presentation once a year, it’s time to reconsider your training strategy. The impact that proper cybersecurity training can have, and who tends to have access to it, is discussed below.
The cloud has allowed managed IT service providers, or MSPs, to fill a uniquely shaped void in many companies’ business models. Working with a managed service provider can make up for all of the traditional challenges of technology maintenance and management while also affording you unique opportunities to limit costs, reduce waste, and increase productivity.
Regardless of your industry, there are going to be certain regulatory standards that you will be responsible for upholding. Many of these standards will be related in some way to your cybersecurity. Some of these cybersecurity standards are listed below, as is why compliance is so imperative for your business.