IT Support Business Models by Macro Systems
Even in its simplest form, a small business is a complex machine. One cog that’s not operating at the appropriate capacity can create operational problems that lead to bigger, more expensive problems later down the road. While businesses worry about the economy and ensuing financial issues, the reality is that your business is far more likely to fail due to operational inefficiencies.
What do you do when you realize you’ve written three sentences of absolute gibberish?
What do most of us do? We lean on the Backspace key. We sit there, staring at the screen, watching the cursor slowly eat away at the alphabet like Pac-Man. The funny thing is that all that holding down the backspace key for five seconds is inefficient, and quite frankly, you’re better than that. It’s time to stop making a fool out of yourself and start tactically deleting your text. Listed below is how you do that:
A client walks into the office, a contractor needs to check a manual, or a visitor is waiting in the lobby, and they ask that ubiquitous question: "What’s the Wi-Fi password?" We've all been there.
Sharing it feels like common courtesy, of course. If you are handing them the password to your primary office network, you are doing much more than sharing an internet connection. You are essentially handing a stranger the keys to your entire digital office.
You’ve probably heard a ton of password advice over the past decade, but how much of it is actually good advice that you should listen to? With modern, advanced automated threats able to crack incredibly complex passwords with ease, you can’t be too careful. You might even need to take a different approach entirely… which brings us to the OG password advice: make it longer.
Does your business operate in the moment, or does it prioritize what’s just around the corner? As a business owner, you have a delicate balance to strike between the two, and where technology is concerned, the answer is not always so clear-cut. But it’s generally better for your business to look at technology management with the perspective offered by an IT roadmap to inform your decision-making, from everyday implementations to major deployments.
If your cloud bill is the second-largest line item after payroll, but you still can’t explain exactly what you’re paying for, you aren’t running a lean operation; you’re paying a significant and ever-expanding growth tax.
For a business owner, cloud tracking isn’t about technical metrics like CPU usage or latency, it’s about margin preservation. It is the difference between scaling your profit and simply scaling your provider’s revenue. If you want to stop the end-of-month heart attack, you need to turn technical voodoo into a manageable business asset.
Does the idea of cybersecurity strike terrify you? We know it’s not every business’ specialty, but that doesn’t make it any less critical for companies like yours to consider. We want to make it as easy as possible for your employees to practice appropriate cybersecurity measures, and that starts with a simple one-page cybersecurity cheat sheet.
We will be the first to admit it: we are obsessed with security.
In an era where cybercriminals are more sophisticated and persistent than ever, that obsession is a necessity. Today's security requires a fundamental shift in mindset: you cannot implicitly trust anyone. Not outside hackers, and, uncomfortable as it may be, not even the people inside your organization.
This trust-no-one approach is the foundation of Zero-Trust Security.
It isn’t rare for business owners to seek out opportunities to trim expenses and cut costs wherever possible. Your security should never be someplace you look… especially if you hope to ever secure the increasingly important business insurance you need.
Now you may be saying, “But my IT is surely good enough.” Alas, that standard isn’t sufficient in the eyes of insurance providers, and as a result, it actually becomes more expensive than having the right technology protections in the first place.
As an IT service provider, our techs spend their days at the intersection of cutting-edge and business-critical. In 2026, the conversation about each has shifted. It is no longer about whether you should utilize AI, because everyone is, but about the risks of trusting it blindly.
We have seen it firsthand: businesses that treat AI like a set-it-and-forget-it solution often end up calling us for emergency damage control. Listed below are the major pitfalls of over-trusting AI and how to keep your business from becoming a cautionary tale.
A backup does not truly exist until you have successfully restored from it; this is the hard truth of information technology. Many business owners and internal teams depend on the green checkmark in their software dashboard to signify safety. However, that status light can be misleading, masking deep-seated issues that only appear when a crisis begins.
With AI now being used by adversaries to reverse-engineer patches and generate exploits in hours rather than weeks, our old Patch Tuesday rhythm is essentially an open invitation to hackers. The truth is, the patching gap is a competitive weakness.
If we want to protect our businesses without drowning our teams in manual toil, we have to stop treating patching as a checklist and start treating it as a dynamic, intelligent discipline. Here is how we’re rethinking the vulnerability situation.
In the late 1990s, computer security was simple: you locked the door to the server room and hoped nobody guessed that the admin password was “admin.”
Fast forward to today, and that is simply unrecognizable. Hoping for the best isn't just a poor strategy, it’s a liability. As you set your business goals for the coming year, it’s time to move past legacy mindsets. Modern protection requires more than just software; it requires a team that is trained, vigilant, and ready to act as your first line of defense.
Modern business technology is like operating in the wild west. It’s expansive, fast-moving, and if you aren’t careful, it can gallop away from you before you even realize it’s gone. Between SaaS sprawl, underutilized hardware, and hidden maintenance fees, many companies are overspending by 20-to-30 percent on their entire technology stack. That’s a lot of money.
It’s time to saddle up and start earning some savings. Listed below is a guide of sorts that can help you round up your expenses and bring your technology budget back under control.
Did you know that, in physics, regardless of how much time, sweat, and energy you put into pushing a boulder, if it doesn’t move, the “work done” is seen as zero? The same is true in business… at the end of the day, your investment in your organization and its people is only worthwhile if you see results.
Thus, you need to ask yourself: how much work are your team members actually getting done? Are they moving the boulder, or are they just trying a lot but not actually making any progress? Below we examine what often leads to this kind of stagnant struggle and how you can fix it.
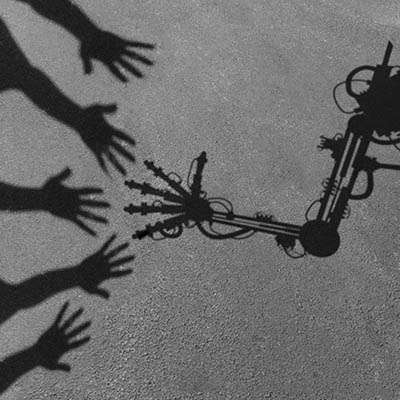
Have you ever stopped to ask yourself if the person you’re talking to on the phone is an AI system or an actual human being? It’s expected that in 2026, you’ll be asking this question a lot more, especially with the rise of agentic AI. This development takes the vulnerability that already exists in your human infrastructure and attempts to make it impossible to stop. Below we’ll explore agentic AI, what it looks like, and what you can do to put a stop to it in the years to come.
Cyberthreats are no longer rare occurrences - they are constant, evolving, and frequently highly sophisticated. This reality makes a proactive approach to cybersecurity absolutely mandatory. Businesses that only react to attacks find themselves perpetually engaged in damage control.
Failing to establish a deliberate, comprehensive cybersecurity strategy exposes any organization to repeated breaches, critical data loss, and ultimately, a loss of customer trust that can lead to financial collapse. This overview details why addressing these persistent risks is critical for the success of any contemporary business.
Technology doesn’t last forever, so what would you do if your keyboard or computer monitor died tomorrow? Some might just throw the technology in the trash and not think twice about it, but that’s the exact opposite of what you should do. Instead, Macro Systems urges you to go through the proper channels to properly dispose of your old electronics—if not for the environment’s sake, then for your business’.