IT Support Business Models by Macro Systems
Cybersecurity is intensely critical, so a business owner would think implementing every security feature and defense would be a good idea. As research has shown, this can be counterproductive, as only 67% of surveyed security leaders know what led to cybersecurity incidents in their businesses over the past year.
The world’s largest ticket retailer is in the headlines for the wrong reasons after their parent company, Live Nation Entertainment, filed an 8-K filing with the Security and Exchange commission admitting that they had been hacked to the tune of 1.3 terabytes of information. That amounts to 560 million customers’ personal information that has been stolen from the company’s servers. Listed below is a look at the hack and what it means for consumers.
Mobile malware isn’t common, but it’s growing increasingly more so. You may have heard of a malware called XLoader, which has been utilized to victimize people in over seven countries. This mobile threat has seen various iterations over the past several years, but you should be especially concerned these days.
If you are old enough to remember when, like most computer software, antivirus came in a large textbook-sized box at the store, then you probably remember a time when that was the only protection you really needed.
These days there are countless free versions of antivirus out there. How much protection do these actually provide, and when and where might they be a good fit?
We’re hoping that you are reading this post to prepare yourself in case your organization were to face a ransomware attack, but if you are suffering from one right now, we encourage you to reach out to us immediately, whether you are a client or not. Ransomware spreads quickly, and once it has infected a system, there really isn’t much you can do to stop it. That being said, there are steps you need to take to come back from this gracefully.
With technology being a vital part of our lives and society, cyberthreats continue to evolve and pose significant risks. One such threat that is on the rise is browser hijacking attacks. Listed below are the dangers of these attacks, including the techniques employed by hackers, and how small and medium-sized businesses can protect themselves.
Ransomware is one of the worst situations that any organization could have to deal with. It not only holds your data or computing infrastructure for ransom, it also creates situations where you have to explain to your clientele that you’ve been breached and that their information has fallen into the hands of scammers looking to extort your business. Listed below are details about how ransomware works and other details to give you an idea of just how unpleasant it is.
Even if mobile malware doesn’t have as much of a presence in the cyber threat landscape as other significant threats like ransomware variants, it is still just as dangerous under the right circumstances. An Android banking malware called Sova, for example, has returned with a vengeance with additional features to make users’ lives miserable.
As a business professional, it’s your responsibility to protect your organization's digital assets from cybercrime, but the path forward is not always so easy or clear-cut. Without a thorough knowledge and expertise of IT security at your disposal, it can be challenging to protect your infrastructure as adequately as it needs to be. Listed below are some of the common problems that involve cybersecurity, as well as how you can address them.
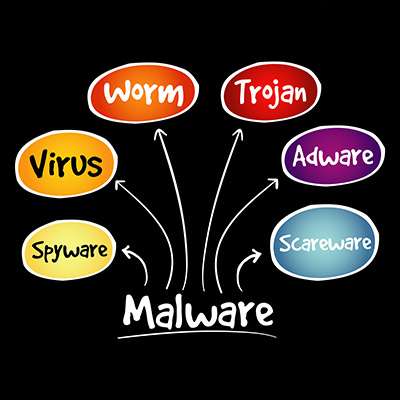
Network security could mean a number of things, but usually people are using the term as a blanket statement against the dreaded idea of malware and its numerous forms. Listed below is a discussion on how vast the world of malware can be and how often you might find yourself misunderstanding what it exactly is. Comprehending all this can help you identify if you have become a malware victim or not.
Ransomware is regarded as one of the worst modern cyberthreats out there, and there's ample evidence to support this. These attacks and their aftereffects can devastate businesses of all industries. Listed below is an explanation about why ransomware is so dangerous, and what can be done to fight it.
Many threats instantly make themselves known on your device the second they install themselves, like ransomware and other kinds of malware. Others, like the newly discovered threat called MosaicLoader, discreetly install themselves in the background of your device and cause issues behind the scenes.
You often hear about malware that infects desktop PCs, laptops, or servers, but other kinds of malware that infect mobile devices also exist. One such malware, a threat called TangleBot, has been discovered, and it can become seriously problematic for both workers and consumers utilizing Android devices, especially in the modern mobile-centric workplace.
The cyberattack on SolarWinds was devastating for many reasons, and Microsoft has officially uncovered yet another kind of malware used in the attack on the software provider: a backdoor threat they have named FoggyWeb. What does this threat do and why is it so imperative to look at this incident even now?