Cybersecurity is a massively critical consideration for modern businesses, and as a result, managing it is often given a considerable amount of time. However, recent developments suggest that this time can potentially be reduced by the use of “self-healing” security software. This may sound a little out there, but stay with us! We’ll explain.
IT Support Business Models by Macro Systems
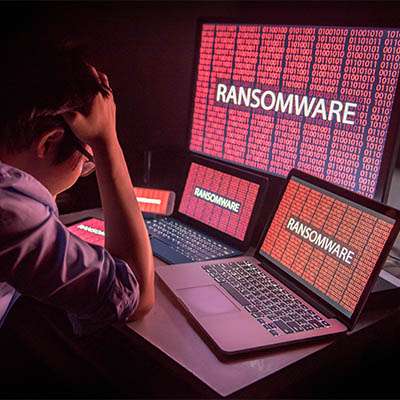
While it only makes sense to assume that a hacker would focus specifically on those targets that would bring them the greatest profit (in other words, larger businesses), the reality of modern cybercrime renders this assumption grossly outdated. Let’s examine how different developments in ransomware have made it possible for hackers to be far less discerning in who they target.
Another ransomware threat is here, this time targeting unpatched and end-of-life products in SonicWall’s Secure Mobile Access (SMA) 100 series and Secure Remote Access (SRA) products. To make things worse, the threat is currently being used, so businesses utilizing these devices must take action now to limit how much damage this ransomware can do.
While the right IT solutions can be a significant advantage to your business and its processes, this will only be the case if your team members are trained to use them properly. Listed below are some of the training that you need to prioritize in order to ensure your team is ready to utilize your technology the way it should be utilized.
Out of all the email messages you get throughout the workday, how many of them are spam messages or malicious emails from hackers? You don’t need us to tell you that spam and phishing emails are a serious problem, but sometimes they can be hard to identify, especially to the untrained or uninformed eye. Listed below are some of the telltale signs of spam and phishing emails, as well as how you should react to them.
Security can be rough for small businesses to optimize, but that does not make it any less imperative. One such way that security can work against you is actually your employees’ predispositions toward it; the cognitive biases that your employees have regarding security can put your business at risk, even if that is the last thing on their minds.
Cybersecurity is one of those components to an IT strategy that is absolutely imperative; you cannot ignore it in the modern age of ransomware and other high-profile hacks. In order to make sure that you are prepared to handle anything that comes your way, you must periodically test your security practices and assess how well your team can prepare for attacks. The question remains as to how often you should do this.
“Hackers are a serious threat to modern businesses” isn’t exactly a novel statement, is it? On the other hand, if a hacker was lurking on your network, would you know the signs to help you catch them? Just in case, we wanted to share a few strategies that can help highlight these warnings so you can more effectively catch any threats present on your network, especially when your workforce is accessing it remotely.
Nothing is more irritating than going to log into your device and finding out that you can't access it or that files you thought were there have been wiped. Alas, this is the situation that many users of a specific device have recently gone through. Thanks to an unpatched vulnerability, users of Western Digital’s My Book network-attached storage device are suffering from lost files and lost account access stemming from remote access.
A new ransomware attack has surfaced, this time mostly targeting IT companies and their clients. The attack is specifically targeting the Kaseya platform. Kaseya is management software that many IT companies utilize to remotely manage and support technology. The attack in question targeted Kaseya’s supply chain via a vulnerability in its VSA software; this attack is notable because of how it targeted the supply chain, not only striking at the vendor’s clients—notably IT companies—but also their customers. Essentially, this attack had a trickle-down effect that is causing widespread chaos for a massive number of businesses.
The last few months have been filled with severe cyberattacks, particularly those taking advantage of major businesses that might not initially be considered targets for these kinds of attacks. For example, McDonald’s Restaurants was recently breached. We examine the situation below, and how it plays into the recent trends we’ve witnessed.
Millions of people find themselves sitting in front of a computer moving files around and corresponding with people over the phone, through email, or updating info in the company’s line of business app. However, what many of them don’t know, is that, at any time, they are only a couple of clicks away from causing significant problems for their organization. This is why it is extremely imperative to train your staff on what to look for and how to address those situations when they do arise.
According to a survey conducted by Splunk and Enterprise Strategy Group, more business leaders plan to funnel funding into their cybersecurity; 88 percent of respondents reported a planned increase into their investments, 35 percent reporting that these boosts will be substantial. Listed below are a few of the insights that this survey has revealed.
Last weekend a significant cyberattack occurred against the world’s largest meat processor and distributor, JBS S.A., that completely shut down the company’s operations in both North America and Australia… and as a result, has affected the supply chains associated with the organization. What lessons can be learned from all this?
Most accounts these days require a password and, as such, the average user has countless of these codes that need to be kept secure. Some web browsers have built-in password management tools to help make them more user-friendly, but with so much convenience involved, one has to ask whether or not these built-in management tools are as secure as they should be.
Most organizations have compliance regulations they need to meet. 2021 is becoming somewhat of a tipping point for some. Businesses are dealing with the development of new data privacy laws that will surely add some responsibilities on top of already established regulations. Below is a look at compliance and why it is critical to stay on top of it.
Ransomware has been a significant problem for the past several years. Once known for breaching networks directly, the establishment of uncrackable encryption left hackers looking to change their strategies. Now they use scams to get people to give them access to network resources. If they are successful, it can deliver more than headaches for a business. Below is a look at what makes ransomware so dangerous and how your business can combat the constant attacks that come your way.
Your organization's data is perhaps its most important resource, which is why it is so critical that it remains protected against all threats (including those that come from within your own business). Consider, for a moment, the ongoing trial of Xiaorong You, going on in Greenville, Tennessee. Accused of stealing trade secrets and committing economic espionage, You allegedly stole various BPA-free technologies from various companies—including Coca-Cola and the Eastman Chemical Company, amongst others—to the tune of $119.6 million.
We always picture hackers as these foreboding, black-clad criminals, smirking through the shadows in their dark room by their computer monitor. Hard, uncaring individuals who don’t go outside very often, staring at code as if they were able to decipher the Matrix.
It’s time we give up this persona and stop mystifying cybercriminals. Why?
It only takes a few dollars and some spare time to truly hold an individual’s data hostage.
Macro Systems likes to remind people as much as we can of the importance of staying up-to-date with your organization’s cybersecurity. There are numerous things you can do to strengthen your grip on your network. This month we thought we’d go over some of the solutions we provide to help our clients secure their network and infrastructure.