Social media scams encompass fraudulent activities and deceptive schemes that occur across numerous social media platforms. These scams target users on platforms like Facebook, X (formerly Twitter), LinkedIn, and various others, irrespective of their age or background. They exploit individuals' trust, curiosity, or lack of awareness. Social media scams manifest in various forms, and the following are some common examples.
IT Support Business Models by Macro Systems
Passwords play a pivotal role in safeguarding an organization's cybersecurity, acting as a vital tool for employees that surpasses the risks of relying on their own memory. Below we delve into the pros and cons of employing password managers to fortify the protection of company-owned digital assets.
One major nonprofit has become the victim of a disclosed major data breach, affecting 890 schools all across the US: the National Student Clearinghouse, or NSC. The organization has announced that they have experienced a significant data breach that has put their clients’ data at risk. What does this mean for affected organizations and their clientele?
Data privacy is absolutely imperative these days in both a business and individual context. In some locations, governments have introduced legislation to protect consumers, and in others, there is significant pushback in favor of fewer regulations on business. How does data privacy factor into your business’ operations?
You might see encryption as a major Advantage to your cybersecurity strategy, but it’s often utilized in a way that might have you guessing whether you really understand it. Listed below is a closer look into what encryption does to your data, as well as why it is essential for any business to ensure maximum privacy and security.
How often does your organization take it upon itself to ensure that those working for its success—your employees—are kept up to speed on cybersecurity? If your approach is to have your team sit in a room and watch a presentation once a year, it’s time to reconsider your training strategy. The impact that proper cybersecurity training can have, and who tends to have access to it, is discussed below.
The United States Federal Trade Commission’s mandate is to prevent fraud and promote consumer protection in today's interconnected world, where the digital landscape continues to evolve at a frenzied pace. The FTC recognizes the importance of safeguarding consumer information and has implemented their Safeguards Rule as a means to ensure that businesses protect sensitive data from unauthorized access and misuse. Listed below is a look at the Safeguards Rule and what you need to know about it in regard to your organization.
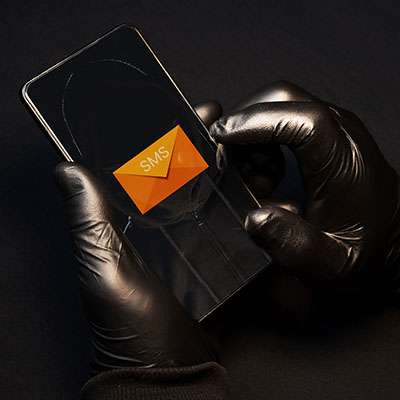
We talk about phishing often here, and one method that usually flies under the radar is smishing, or phishing that is conducted via SMS messages. Although email phishing is perhaps the most common method of conducting these scams, you should also be prepared to take on smishing, as it comes with its own share of unique challenges and dangers.
These days you can’t afford not to have some portion of your business’ budget set aside for cybersecurity. The question is, how much do you need, and what should you be spending it on first? Let’s take a few moments to dig a little deeper into this question and examine a few cybersecurity protections you should establish as your business’ baseline defenses.
Your business has to promote security whenever it can. In terms of keeping your wireless connections secure, the thought behind it is that if unauthorized people and machines can access your network without protections, they can do whatever they want with the data on the network. This is a significant problem. Listed below are a few things you need to consider to keep your wireless network secure.
There is a lot of misinformation and misperceptions related to network security out there, especially concerning small businesses. In particular, browser security is one aspect where many individuals’ knowledge simply falls flat, and they buy into myths that put their data at risk. Listed below is an attempt clear up some of these misconceptions so you can go about your day in a more secure way.
Businesses can't afford to grow complacent with their network security; it could make a significant difference between falling prey to an attack and remaining secure. The process of securing a network must be looked at holistically, from top to bottom. This idea of enterprise security is not new, but even a small business needs to keep it in mind, and these solutions are more accessible than you might think.