Do you realize how the countless devices entering the workplace will influence your business’s infrastructure and security? It’s imperative to remain aware about how the Internet of Things and connected devices will affect your business in the near future. According to HAX Hardware Trends, 2018 will see a string of changes in how we approach the Internet of Things, as well as how businesses govern it for their networks.
IT Support Business Models by Macro Systems
Excel is the primary spreadsheet builder and is tremendously valuable to your business. Spreadsheets are perfect for showcasing information in a compact manner, but without a couple of charts, your users will just be staring at cell after cell of dull old numbers. By using charts in Excel, you can take your spreadsheet building to the next level.
During Christmas, technology is unavoidable. Traditionally, the holidays were a time when things slowed down for companies, people spent time with their families, and business was put on the back burner. Those days are over. The modern professional is lucky to get a day off for Christmas; and, because of the way business works today, may be asked to do more than ever around the holidays.
There are not many security problems that are more dangerous than a network breach. Considering how much you could lose from an unexpected run-in with a hacker, it’s not a surprise that companies are worried. Somehow, even some of the most troubling threats like phishing attacks are often overlooked. A new study introduces the groundbreaking thought that phishing attacks should be at the front of a business owner’s mind regarding network security.

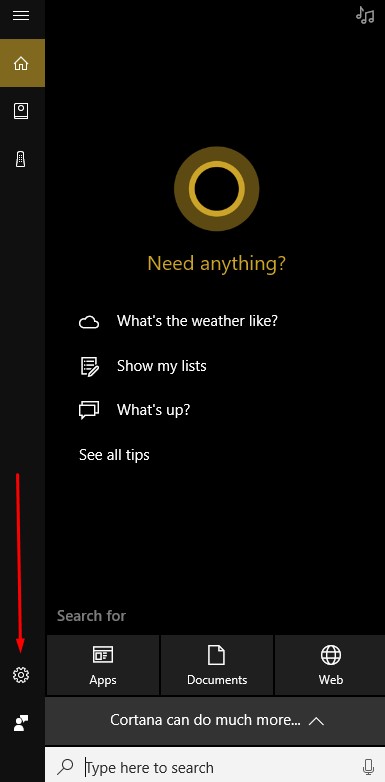
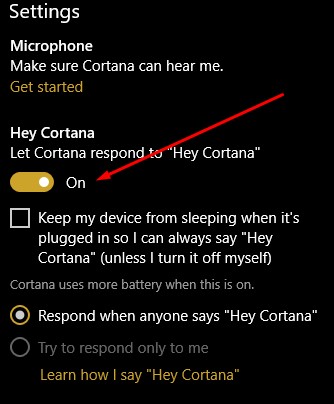
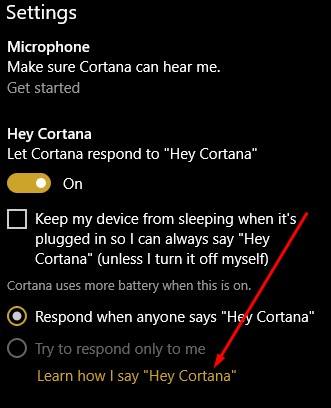
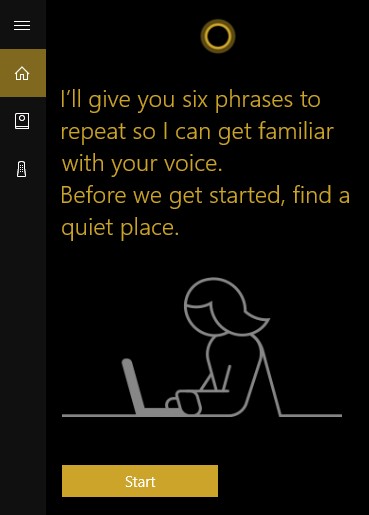
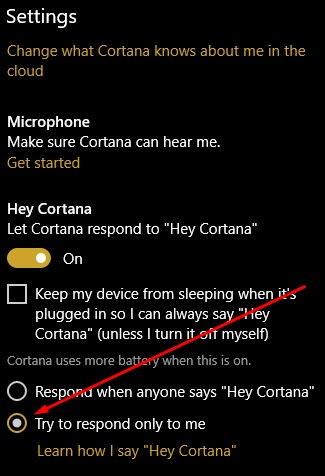
Cortana, Windows 10’s built-in personal assistant, has demonstarted her usefulness for those users who have taken advantage of her services. Occasionally, however, the Cortana interface will answer when another person in the room beckons her. For Cortana to work for one person, and to obey only one voice, the software needs to become familiar with that voice.
An organization's Backup and Recovery strategy is one of the most important aspects of managing a business, especially in a world where more hackers seem to appear everyday and critical mistakes can happen in the blink of an eye. Do you know how to assure that your business is as secure as possible in the event of a disaster? A good place to start is understanding the various terminology associated with data backup and disaster recovery.
Mobile devices have become invavluable in the modern workplace. It'd be difficult to locate a company that doesn’t use smartphones or tablets in some manner. However, mobile devices will never be truly mobile while they need to be tethered to wires plugged into outlets or USB cables due to batteries losing their charges. An innovation called wireless charging has attempted to shake this concept up, but has it proven successful? And what is wireless charging, exactly?
Would your company fall apart if communications were interrupted? This is one of the significant pitfalls that businesses have to deal with, as without formal teamwork and communication, operations can fall apart and productivity can plummet. What are some of the ways that your company manages the numerous modes of communication that it relies on?
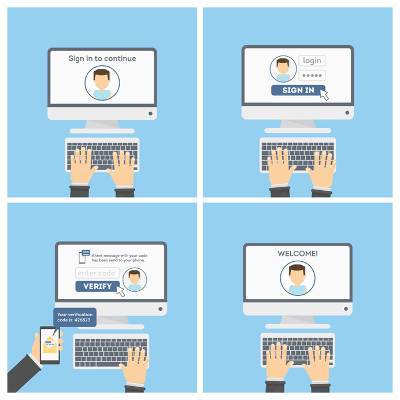
Data security has to be an absolutely critical consideration of the modern business, so every small step you can take to protect your business is important. One such step is the implementation of two-factor authentication. Warning: your employees may not initially feel very comfortable with some facets of two-factor authentication.
Email is such a familiar solution that most people don’t think twice about how it works. However, it’s critical that you at least understand the concept, as it can provide you with a substantial advantage when it comes time to optimize email access on your mobile devices. Let us discuss the ways in which the two major message exchange protocols differ, and then look into the specifics of why you should choose one over the other.
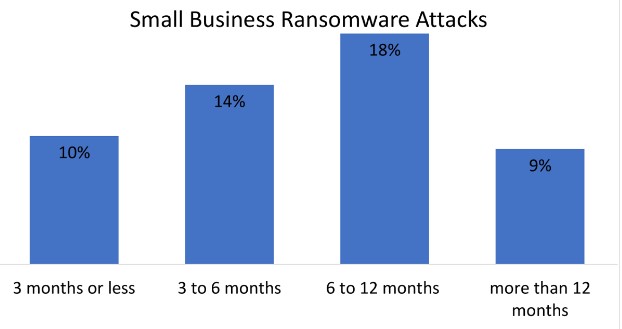
Network security is a crucial consideration for every single organization, especially ones that utilize the Internet. There were a lot of negatives and some positives that came out of 2017 in regards to cybersecurity. Listed below are some of the most troubling cybersecurity statistics collected in 2017, as well as suggestions on how to keep your company safe in 2018.
It's reasonable that people may see having a credit card stolen as identity theft, but that is an oversimplification that can prove dangerous. While credit card theft is an element of identity theft, equating the two means that other forms of identity theft are overlooked. Let's go over why identity theft and credit card theft are not the same thing, and what you can do to help keep your business safe.
Insider dangers contribute to a remarkable number of data breaches. These cases of data vulnerability are permitted by a member of your workforce, whether they intended to harm your business or simply made an honest mistake. With so much focus directed toward the dangerss out in the world, sometimes we forget that the biggest threats can be among our ranks. Here are a few ways to keep insider dangers from doing your business significant harm.
The computer an individual owns or uses for work is mostly just a machine used to execute specific tasks. This doesn’t mean that the individual shouldn’t know all of the modern tips that help you get the most out of it, though. Here are some of the best shortcuts that you can use to take full advantage of your workstation.
Collaboration is a critical aspect of business these days, which has led to many developers and providers entering the business of collaboration. These developers are in extensive competition with each other trying to update their offering so it's better than the others. Recently, Facebook Workplace, Slack, and Google’s Gmail each received collaboration-boosting updates.
With the increasing popularity of Cyber Monday sales, employees are probably tempted to shop during while 'on the clock'. There are numerous promotions exclusively available to online shoppers that take place during a business’ hour of operations. Most organizations allow occasional use of company time for personal use. Inevitably though some employees are going to take advantage of this generosity and abuse the privilege.
For businesses everywhere, technology is a necessity to reach their goals, which are of course influenced by the technology that companies are able to access. For this cycle to continue, a business needs to establish what is expected to come next in the line of IT innovation. It seems companies are currently placing convenience as a priority.
As holidays approach, most workers are unsure whether they will be able to spend their time at home with their families, or be stuck at the office trying to beat a critical deadline. The increase in mobile technology hasn’t made getting away from work any easier, but it has made it easier to work away from the office. How can you achieve a solid work/life balance?