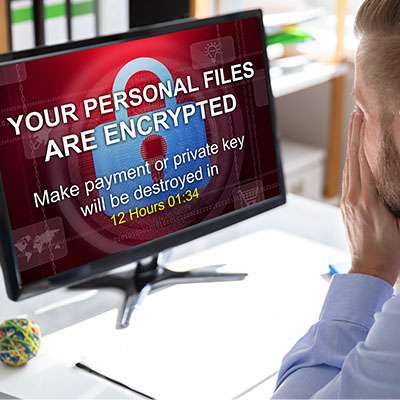
“I don’t need to worry about cyberattacks… my business is too small to be of any interest.”
This brief rationalization is one of the most dangerous fallacies a modern business can make concerning cybersecurity; it shows a fundamental misunderstanding of how modern cyberthreats operate. If this has been your mindset, we urge you to read on so we can help set you on a more realistic path.