We’ve all seen our friends and family sharing quizzes on their social media profiles, prompting people to find out what their celebrity stage name or what Hogwarts house you would be in. These fun, lighthearted quizzes are a solid way to get to know a little more about the people we’re connected with… and that’s the biggest issue.
IT Support Business Models by Macro Systems
Gauging the effectiveness of your cybersecurity can be a daunting task, especially when asking if it could make a significant difference in protecting your organization’s network infrastructure. If you want to track and measure your business’ cybersecurity preparedness, here are four steps to help you perform an evaluation.
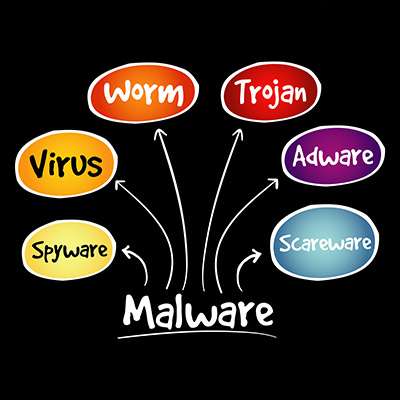
Network security could mean a number of things, but usually people are using the term as a blanket statement against the dreaded idea of malware and its numerous forms. Listed below is a discussion on how vast the world of malware can be and how often you might find yourself misunderstanding what it exactly is. Comprehending all this can help you identify if you have become a malware victim or not.
Cybersecurity is an important subject for a business’ entire team to appreciate, particularly when it comes to the minute differences between different terms. For instance, a layperson might hear “breach” and automatically think “security incident.” While this technically isn’t incorrect, per se, the two terms aren’t really synonymous.
Let’s take a few moments to dive into the minutiae and define these two terms more clearly.
More workplaces are utilizing the power of remote technology, but this also creates issues with security that must be addressed. How can you ensure that your business isn’t putting itself at risk as a result of this general displacement of your workforce? Listed below are some action items you might choose to implement for your organization.
When we talk about data privacy in a business, the default is to usually think about the data the business has collected and compiled from its clientele. On the other hand, that’s just one type of data a business has. There’s also a lot of data that is collected by the business about that business’ employees. So, how well protected is this data?
Ransomware is regarded as one of the worst modern cyberthreats out there, and there's ample evidence to support this. These attacks and their aftereffects can devastate businesses of all industries. Listed below is an explanation about why ransomware is so dangerous, and what can be done to fight it.
There are times when you have computer issues and you might hesitate to call in the big guns to resolve the problems. Alas, the reality is that many businesses are under the impression that calling experts to handle their computer problems will leave them in a difficult position financially. Macro Systems is here to make sure that doesn’t happen! Listed below are three common computer repair problems that you may be able to solve in a simple and easy way.
If there is one shared priority most businesses need to have it’s a strategy on how they are going to go about securing their network, infrastructure, and data from the numerous threats they face. Listed below is a look at three of the most imperative issues surrounding organizational cybersecurity as we head into the new year.
Smart devices and Internet-of-Things devices in general have taken the world by storm, and a home without at least a handful of smart devices is quite rare to find these days. On the other hand, smart devices (devices that connect to the Internet to perform various functions) must be approached with a certain level of caution.
The holiday season has a variety of famous key players, including Santa, Rudolph, and the rest of the North Pole crew. Each year, they use their magic to help spread goodwill and joy to all the nice children of the world… but did you know that they are also responsible for protecting those who make the naughty list from Santa’s villainous counterpart, Krampus?
As the official managed service provider for Santa’s operation, we have been cleared to share the story about how we’ve helped defy Krampus to save Christmas.
It's very simple: Ransomware is very bad. The first half of 2021 saw a massive increase in ransomware attacks that made the lives of countless individuals and business professionals difficult. On the other hand, a new trend is surfacing, and it’s one that you might be surprised to see: fake ransomware threats.
Twitch, Amazon’s popular streaming service where gamers and content creators broadcast to wide audiences, recently endured a data breach. Due to this data breach, folks on the Internet now know just how much these content creators make, and it has exposed a whole new problem that Amazon must resolve.
Many threats instantly make themselves known on your device the second they install themselves, like ransomware and other kinds of malware. Others, like the newly discovered threat called MosaicLoader, discreetly install themselves in the background of your device and cause issues behind the scenes.
Even the most cautious employee could fall victim to a well-placed phishing email. What are some factors that contribute to the success of these cyberattacks, and what subject lines in particular should people be cautious about? A recent study takes a look at what goes into a successful phishing attack, and you might be surprised by the results.
You often hear about malware that infects desktop PCs, laptops, or servers, but other kinds of malware that infect mobile devices also exist. One such malware, a threat called TangleBot, has been discovered, and it can become seriously problematic for both workers and consumers utilizing Android devices, especially in the modern mobile-centric workplace.
It can be easy to overlook the importance of technology and its security, especially in industries that are deeply steeped in tradition, regardless of how imperative that security may seem when actually considered. Just consider the modern law firm, where technology, data, and the security of such is paramount.